Identity-First Zero Trust Security: The 2026 Definitive Guide
Identity-first zero trust security the dissolution of the traditional network perimeter has forced a fundamental reckoning within the field of cybersecurity. For decades, the “Castle and Moat” strategy—securing a hard exterior while assuming trust for anyone inside—sufficed for centralized, office-bound environments. However, the surge in distributed work, multi-cloud ecosystems, and the proliferation of non-human entities like service accounts and API keys has rendered IP-based security obsolete. In this decentralized landscape, the network is no longer a reliable boundary; instead, the individual entity, or “Identity,” has become the only remaining consistent perimeter.
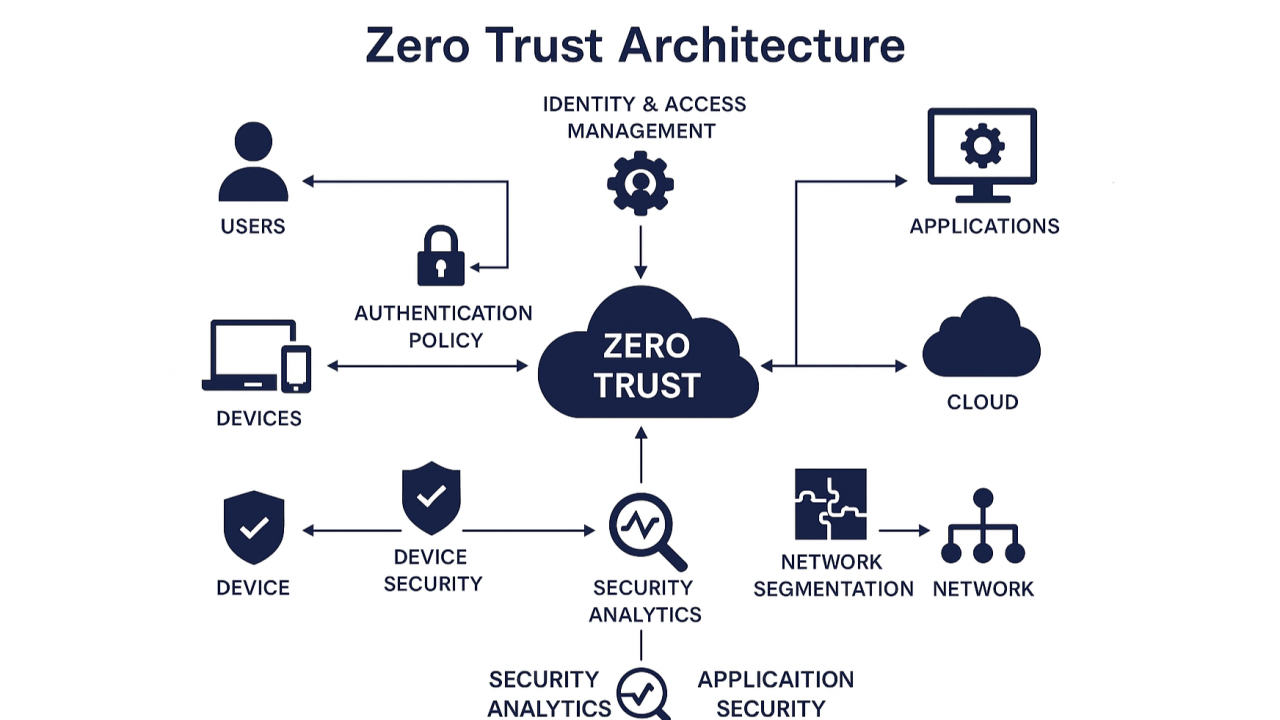
This shift toward an identity-centric model represents more than a technical upgrade; it is a philosophical pivot. It assumes that the network is perpetually hostile and that every access request, regardless of its origin, must be verified, authenticated, and authorized based on a dynamic set of signals. While early Zero Trust implementations focused heavily on micro-segmentation and software-defined perimeters, the industry has realized that without a robust, verified identity at the core, these network controls are merely hollow shells. If a malicious actor compromises a set of credentials, they can bypass even the most sophisticated network segment unless the system can differentiate between a “valid credential” and a “trusted user.“
Implementing a security posture that prioritizes identity requires an architectural overhaul that integrates human resources data, device health, behavioral biometrics, and contextual metadata into a single, real-time decision engine. It demands that we move past the concept of a “static login” and toward a “continuous authorization” model. This inquiry explores the deep structural logic of this transition, examining the nuances of how entities—both human and machine—interact with resources in a world where trust is never inherent.
Identity-First Zero Trust Security
Identity-first zero trust security to master Identity-First Zero Trust Security, one must recognize that “Identity” is not merely a username and password; it is a complex, multi-dimensional construct. It is the practice of securing the “Who” and “What” before addressing the “How” of the connection.
Multi-Perspective Explanation
From the perspective of an Identity and Access Management (IAM) architect, the focus is on the “Source of Truth”—ensuring that the lifecycle of an identity is synchronized across HR systems, directories, and cloud providers. the model is about “Contextual Enrichment,” using signals like impossible travel, device compliance, and typing cadence to build a risk score. From a business leadership perspective, it is a “Friction Management” challenge, balancing high-assurance security with the need for a seamless user experience that does not impede productivity.
Oversimplification and Risks Identity-First Zero Trust Security
A recurring oversimplification is that “Identity-First” is synonymous with “MFA (Multi-Factor Authentication).” While MFA is a critical component, it is a point-in-time check. A true identity-first posture requires “Continuous Adaptive Trust,” where the system monitors the session after the initial login. The danger of an under-engineered identity strategy is “Identity Sprawl,” where fragmented identities across different silos create blind spots that attackers can exploit to move laterally across an organization.
Deep Contextual Background: The Identity Evolution
The trajectory of digital identity has moved through several distinct phases, mirroring the complexity of the systems they protect. In the “Siloed Era,” each application had its own local database of users, leading to the “Password Fatigue” of the early 2000s. This gave way to the “Federated Era,” characterized by protocols like SAML and OIDC, which allowed for Single Sign-On (SSO) and centralized directory services like Active Directory.
However, even federated identity remained anchored to the network. As organizations migrated to the cloud, the “Directory” became a target. The 2026 landscape is defined by the “Decentralized and Machine-First” era. We are no longer just managing employees; we are managing thousands of ephemeral microservices, IoT devices, and external contractors. This evolution represents the transition from managing “Accounts” to managing “Entitlements” at a granular level.
Conceptual Frameworks and Mental Models Identity-First Zero Trust Security
To analyze identity-centric security with professional depth, the following mental models are essential:
1. The “Signal-to-Policy” Pipeline
This framework views every access request as raw data that must be processed through a policy engine. The signals include Identity (who is it?), Device (is it managed?), Context (where/when?), and Risk (what is the behavior?). The output is a binary decision: Allow or Deny. A robust architecture ensures that the “Policy Engine” is decoupled from the application, allowing for centralized changes that propagate instantly.
2. The “Least Privilege” Entropy Model
Access tends toward “Entropy”—over time, users accumulate more permissions than they need (permission creep). This framework mandates a “Zero-Base Entitlement” approach, where access is granted “Just-in-Time” (JIT) and for “Just-Enough-Administration” (JEA). When the task is complete, the privilege is automatically revoked, reducing the “Standing Risk” of the identity.
3. The “Machine Identity” Parity
In a modern ecosystem, machine-to-machine traffic often exceeds human traffic. This model argues that service accounts and workloads must be treated with the same rigor as human users. This involves rotating secrets, using short-lived certificates, and ensuring that every workload has a “Workload Identity” that is cryptographically verifiable, rather than relying on shared API keys.
Key Categories: Humans, Machines, and Workloads
Securing an identity-first environment requires a taxonomy of entities, each with distinct trade-offs and management strategies.
Realistic Decision Logic
For a developer accessing a production database, the system should demand “Phishing-Resistant MFA” (such as FIDO2 keys) and a managed device check. For a customer checking a loyalty balance, a simple “Magic Link” via email provides the necessary low-friction experience while maintaining a basic level of identity verification.
Detailed Real-World Scenarios identity-first zero trust security
Scenario 1: The “Impossible Travel” Alert
A user logs in from New York at 9:00 AM. At 10:15 AM, the same credentials are used to access a sensitive HR portal from an IP address in Singapore.
-
The Identity-First Response: The policy engine calculates an “Impossible Travel” risk score. Because the behavior deviates from the established “Identity Baseline,” the system automatically terminates the session and requires a fresh biometric re-verification on a registered mobile device.
Scenario 2: The “Over-Privileged” Service Account
A legacy script is used to migrate data between two cloud storage buckets.
-
The Failure Mode: The service account has “Administrator” rights to the entire cloud environment. An attacker compromises the script and uses the account to delete backups.
-
The Zero Trust Solution: Utilizing “Workload Identity Federation,” the script is given a short-lived token that is scoped only to the specific two buckets for the duration of the migration. Once the script finishes, the token expires, leaving nothing for an attacker to steal.
Planning, Cost, and Resource Dynamics
The implementation of identity-centric security is a “Hard Cost” in terms of licensing, but it provides a massive “Soft Saving” by reducing the blast radius of breaches.
Resource Impact and Variability
Tools, Strategies, and Support Systems
A high-functioning identity-first stack utilizes several key architectural components:
-
Identity Orchestration Platforms: Tools that sit between various identity providers (IdPs), allowing for a unified policy regardless of whether the user is in Azure AD, Okta, or a legacy LDAP directory.
-
Conditional Access Policies: The “Brain” of the operation, where rules are defined (e.g., “If User is in Finance AND Device is Unmanaged, then REQUIRE MFA AND BLOCK High-Impact Apps”).
-
Phishing-Resistant MFA: Moving away from SMS and push notifications toward hardware keys (YubiKeys) or platform-based biometrics (Windows Hello/TouchID) that are tied to the domain.
-
Identity Threat Detection & Response (ITDR): Specialized tools that monitor for anomalous identity behavior, such as “Golden Ticket” attacks or mass entitlement changes.
-
Privileged Access Management (PAM): Systems that “Vault” administrative credentials and provide “One-Time Use” passwords for sensitive infrastructure tasks.
-
Unified Endpoint Management (UEM): Ensuring the “Device Identity” is verified, checking for OS patches, disk encryption, and the presence of EDR (Endpoint Detection and Response) tools before granting access.
-
Secrets Management: Using centralized vaults (like HashiCorp Vault) to remove hard-coded passwords from code and replace them with dynamic, identity-based secrets.
Risk Landscape and Failure Modes Identity-First Zero Trust Security
Even the most advanced identity systems are vulnerable to “Logical Failures” and “Social Engineering.“
-
MFA Prompt Bombing: Attackers send hundreds of push notifications until a frustrated user finally clicks “Approve.” This is mitigated by “Number Matching” or switching to hardware-bound credentials.
-
Identity Provider (IdP) Compromise: If the central directory is breached, the attacker “Owns” the keys to the kingdom. This requires “Tiered Administration” and offline backup of the root identity keys.
-
The “Ghost User” Mode: Service accounts created for a specific project that is now finished, but the accounts remain active and unmonitored.
Governance, Maintenance, and Long-Term Adaptation
Identity is not a static state; it is a “Lifecycle Management” discipline.
-
Review Cycles: Quarterly “Access Reviews” where managers must explicitly re-approve the permissions of their team members. Any un-reviewed access is automatically revoked (“Deny by Default”).
-
Adjustment Triggers: A change in an employee’s “Department” or “Job Title” in the HR system should trigger an immediate “Re-Evaluation” of their access permissions.
-
The Layered Checklist:
-
Continuous: Monitor for “Shadow IT”—users using their personal identities to log into corporate resources.
-
Annually: Conduct an “Identity Perimeter” test, attempting to bypass controls using leaked credentials.
-
Measurement, Tracking, and Evaluation
How do you measure the efficacy of Identity-First Zero Trust Security?
-
Leading Indicators: “MFA Adoption Rate” for sensitive apps and “Mean Time to Revoke” access for departing employees.
-
Lagging Indicators: Number of “Lateral Movement” attempts blocked and the “Blast Radius” of a single credential compromise.
-
Documentation Examples:
-
Entitlement Map: A visual representation showing who has access to what, and why.
-
Risk Signal Log: A detailed record of why specific access requests were challenged or denied.
-
Common Misconceptions and Industry Myths
-
Myth: “Single Sign-On (SSO) makes us less secure by providing a single point of failure.“
-
Reality: SSO provides a “Single Point of Control,” allowing for stronger MFA and centralized logging that would be impossible with siloed logins.
-
-
Myth: “Machine identities don’t need MFA.“
-
Reality: While machines don’t use “factors” like humans, they require “Multi-Signal Verification” (e.g., Certificate + IP + Signed Workload Identity).
-
-
Myth: “Zero Trust is a product you can buy.“
-
Reality: Zero Trust is a strategy. You can buy tools that support it, but the “Identity-First” part requires process and policy changes.
-
-
Myth: “Biometrics are unhackable.“
-
Reality: Biometrics can be “Spoofed” or bypassed at the software level. They must be combined with “Device Trust” to be effective.
-
Ethical and Practical Considerations Identity-First Zero Trust Security
The move toward pervasive identity tracking raises significant “Privacy” and “Consent” concerns. A professional human editor would argue that “Security should not come at the cost of dignity.” The goal of an identity-centric posture is to protect the user’s digital persona, not to surveil their every move. Finding the “Golden Ratio” between high-assurance security and user privacy is the ethical challenge of the next decade.
Conclusion
The transition to Identity-First Zero Trust Security is the inevitable response to a world without boundaries. It is a recognition that in the digital realm, “Identity” is the only thing we can truly verify. By decoupling security from the network and anchoring it to the entity, organizations can build environments that are both highly resilient and fundamentally adaptable. The future of security is not in the moat, but in the verified integrity of the individual at the gate.






